Alberto Dainotti

NOTE to students: All TA slots for my 2025/2026 classes have been already assigned. I cannot hire more TAs.
Associate Professor — School of Computer Science
Adjunct Professor — School of Cybersecurity & Privacy
Director of the Internet Intelligence Lab
Georgia Tech
Office: Klaus Advanced Computer Building, room 3336
Email: dainotti AT gatech DOT edu
Visiting Faculty Researcher
Google
Google Scholar
Curriculum Vitae
Full publication list
in chronological order, or
by topic, or
by journal/conf/editorial
Updates
 For fresher updates check out my lab's webpage: Internet Intelligence Lab
For fresher updates check out my lab's webpage: Internet Intelligence Lab
[Aug 2023] Our paper on detecting forged-origin BGP hijacks was accepted at NSDI 2024.
[Aug 2023] Our paper on building a network "meta-telescope" was accepted at IMC 2023.
[May 2023] Our inter-disciplinary paper on Internet connectivity shutdowns was accepted at SIGCOMM 2023.
[Apr 2023] Congrats to Aniket! His paper characterizing aggressive Internet scanners was accepted at CoNEXT 2023.
[Mar 2023] Congrats to Zhiyi! His paper won the Best Community Artifact Award at PAM 2023.
[Nov 2022] The Broadband Internet Technical Advisory Group (BITAG) published a “Security of the Internet’s Routing Infrastructure” report, to which I contributed.
[Oct 2022] The Organisation for Economic Co-operation and Development (OECD) published a report on “Routing security: BGP incidents, mitigation techniques and policy actions”, to which I provided input.
[Jul 2022] We had two papers accepted at IMC 2022.
[Jul 2022] Our study in collaboration with UCSD on the feasibility of physical attacks on Internet Access Networks will appear at USENIX Security 2023.
[Apr 2022] The Journal of Information Technology & Policy published our study—led by Lukas Kawerau @ U. Konstanz—where we show use of selective censorship techniques by autocrats.
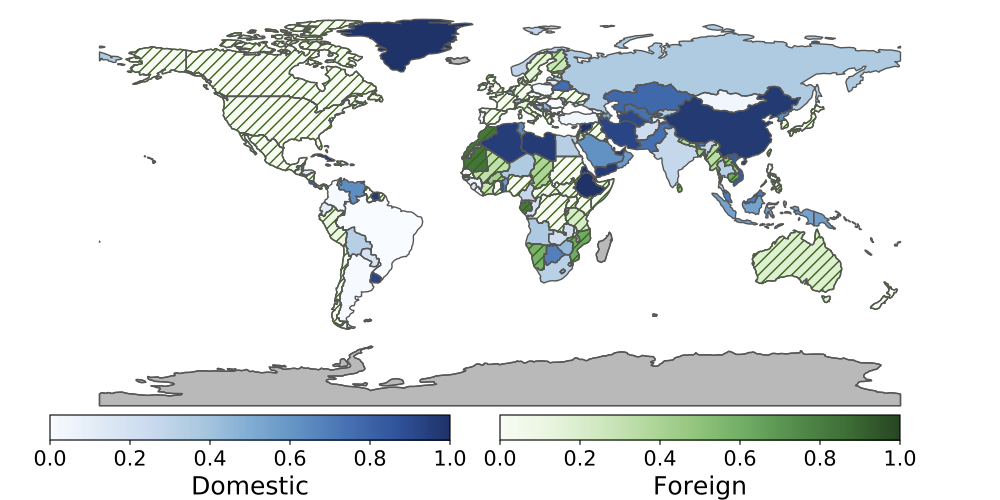
[Mar 2022] "Quantifying Nations’ Exposure to Traffic Observation and Selective Tampering". DOUBLE Congrats to Alex for getting a key paper from his PhD thesis accepted at PAM 2022 and for the paper receiving the Best Dataset Award!
[Jan 2022] This spring I will teach Internet Data Science (CS 8803)
[Nov 2021] Our paper on two-phase scanners has been accepted at USENIX Security 2022.
[Oct 2021] We had two papers accepted at IMC 2021.
[Sep 2021] WIRED UK published a detailed article on Internet shutdowns with several quotes from our team and explaining IODA measurements in layman's terms.
[Nov 2020] Amnesty International published A Web of Impunity: The killings Iran’s internet shutdown hid. I'm humbled that our IODA project contributed to this investigation highlighting the human rights costs of Internet shutdowns.
[Oct 2020] Many congrats to Rama for leading our paper on IPv4 and IPv6 address assignment practices that was accepted at CoNEXT 2020
[Aug 2020] We had two papers accepted at IMC 2020.
[Feb 2020] Data from our IODA project was featured in an article from the Wall Street Journal on Internet shutdowns.
[Dec 2019] We had two papers accepted at PAM 2020.
[Oct 2019] We received the IMC distinguished paper award for our study on identifying serial BGP hijackers.
[Jul 2019] Our study investigating use of DoS attacks during elections in autocracies has been published in the Journal of Conflict Resolution. Great multidisciplinary team. Some ideas developed during IMAPS Workshops. Many congrats @philutsc
[Jul 2019] Our paper on identifying Serial BGP Hijackers has been accepted at IMC 2019. Congrats especially to Cecilia@MIT for leading this work.
[Jul 2019] Check out our work on detecting anycast prefixes using only passive BGP data analysis just published on ACM SIGCOMM CCR. Congrats especially to @Ru1B1an and @haoscs, who btw is starting as Asst Prof. @ODU.
[Apr 2019] We had three papers accepted at TMA 2019!
[Dec 2018] Our paper on identifying correlated Internet connectivity failures was accepted to PAM '19.
[Dec 2018] Our Blink paper was accepted to USENIX NSDI '19.
[Aug 2018] Our ARTEMIS paper was accepted to IEEE/ACM Transactions on Networking.
[Aug 2018] Our paper on DoS attacks and BGP blackholing was accepted to IMC.
[Dec 2017] I'll serve as general co-chair for CoNEXT 2018 in Crete, GR together with Xenofontas Dimitropoulos.
[Nov 2017] Our work on inferring Carrier-Grade Deployments using passive measurements was accepted to IEEE INFOCOM 2018.
[Aug 2017] "Millions of Targets Under Attack: a Macroscopic Characterization of the DoS Ecosystem" accepted at IMC 2017
[May 2017] "SWIFT: Predictive Fast Reroute" accepted at ACM SIGCOMM 2017!!
[Jan 2017] I'll be co-chairing the ACM SIGCOMM 2017 Workshop on Big Data Analytics and Machine Learning for Data Communication Networks (Big-DAMA 2017). Consider submitting a paper!
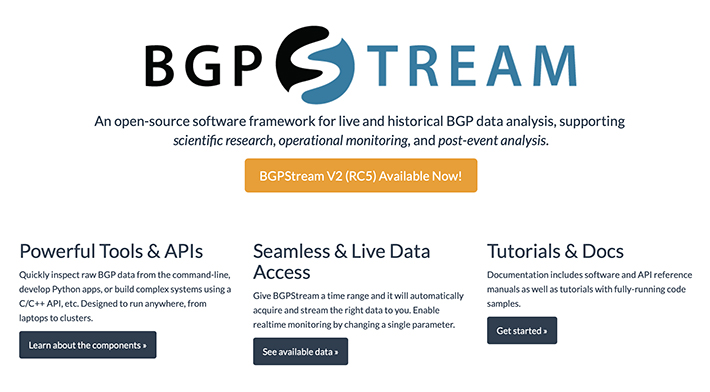
[Dec 2016] Alistair has been awarded the 2017 IRTF Applied Networking Research Prize for our IMC paper on BGPStream!
[Jul 2016] I have been awarded a research grant from Cisco Systems for our work on BGPStream and to collaborate with them to add native support to OpenBMP.
[Jul 2016] Our paper on BGPStream will appear at IMC 2016. (pdf)
[Jul 2016] Read about the CAIDA BGP Hackathon 2016 on ACM SIGCOMM CCR.
[Feb 2016] I'm organizing the 1st CAIDA BGP Hackathon together with USC, RIPE NCC, Route Views, FORTH, UFMG.
[Nov 2015] Check out my invited talk at IETF 94 Measuring and Monitoring BGP
[Nov 2015] We just released BGPStream v1.0
[Sep 2015] Check out our latest paper at IMC 2015 on Leveraging Internet Background Radiation for Opportunistic Network Analysis
[Apr 2015] We published a follow-up analysis of the sipscan at TMA 2015: How Dangerous Is Internet Scanning? A Measurement Study of the Aftermath of an Internet-Wide Scan
[Dec 2014] North Korea got disconnected from the Internet a few times in the last days of 2014. We published a live graph of its BGP reachability status as a preview of our work on detecting and characterizing Internet outages
[Oct 2014] We published a technical report on our Internet census
[Aug 2014] Check our blog post about the recent Time Warner Cable outage
[Aug 2014] Submit your paper to the special issue on the International Journal of Network Management on ``Measure, Detect and Mitigate: Challenges and Trends in Network Security'' (Deadline 1st of December)
[Aug 2014] Our paper on discovering network tarpits in collaboration with Lance and Rob @ CMAND @ NPS was accepted at the Annual Computer Security Applications Conference (ACSAC), 2014.
[Jan 2014] New estimates of IPv4 address space usage in our paper accepted at ACM SIGCOMM CCR: ``Estimating Internet address space usage through passive measurements''
[May 2013]
Check out our blog
post about the scans from the Carna botnet. Cited also by WIRED (link)
[Dec 2012/Mar 2013]
USENIX published the video
of my invited talk at USENIX LISA '12 and also a report of
it in USENIX Login magazine
[Dec 2012]
Check out our blog
post on observing the Syrian Internet blackout from the UCSD Network Telescope
[Sep 2012]
Our research activity on Internet outages has been covered in September issue of Communications
of the ACM Magazine (link)
..more press coverage also at Heise
Online (if you can read Deutsch)
[Jul 2012] Our paper ``Analysis of a "/0" Stealth Scan from a Botnet'' has been accepted at IMC 2012
[Jun 2012] Our work on exploiting malware traffic pollution for detecting and analyzing Internet outages has been awarded as one of the three best papers in ACM SIGCOMM Computer Communication Review of the past 12 months. I will present it in a special session at SIGCOMM 2012
[Jun 2012] I've been awarded the IRTF Applied Networking Research Prize 2012 (link)
[Mar 2012] We've been "press-released" :) And covered by the WSJ blog, among others
[Jan 2012] Our work on exploiting malware traffic pollution for detecting and analyzing Internet outages has been published on ACM SIGCOMM Computer Communication Review, January 2012
[Jan 2012] Our paper entitled "Issues and Future Directions in Traffic Classification" has been published on IEEE Network, January 2012
[Nov 2011] Our work on the Internet "kill switch" in Libya and Egypt has been presented at IMC 2011, Berlin, November 2011
About me
I am an Associate Professor in the School of Computer Science at the College of Computing at Georgia Tech, where I lead the Internet Intelligence Lab. I also have an adjunct appointment at the School of Cybersecurity & Privacy. My research is at the intersection of Internet measurement, data science and cybersecurity. I am interested in understanding when and how Internet infrastructure can fail and proposing remedies. To this end, I develop methods and build near-real-time streaming data analytics systems (IODA, BGPStream, GRIP) that combine diverse data to monitor and improve Internet infrastructure security and reliability. I am also interested in understanding socio-political motivations and implications of Internet cybersecurity events and phenomena. Before joining Georgia Tech I was an Associate Research Scientist and Principal Investigator at CAIDA, the Center for Applied Internet Data Analysis at the San Diego Supercomputer Center, University of California San Diego. I received my Ph.D. in Computer Engineering and Systems at University of Napoli "Federico II", Italy, in 2008.
Research Interests
-
Internet Connectivity Outages
-
Internet Routing Security and Monitoring
-
Cybersecurity & Political Events
-
Address Space Utilization and Structure
-
DoS Attacks, Botnets and Internet Malware
Projects
 |
|
 |
| BGPStream: open source tools and APIs (Python, C) for realtime BGP streaming analytics. Used by researchers and industry. Get v2 now! |
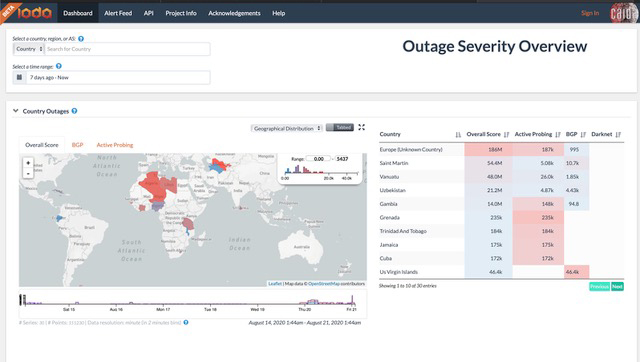
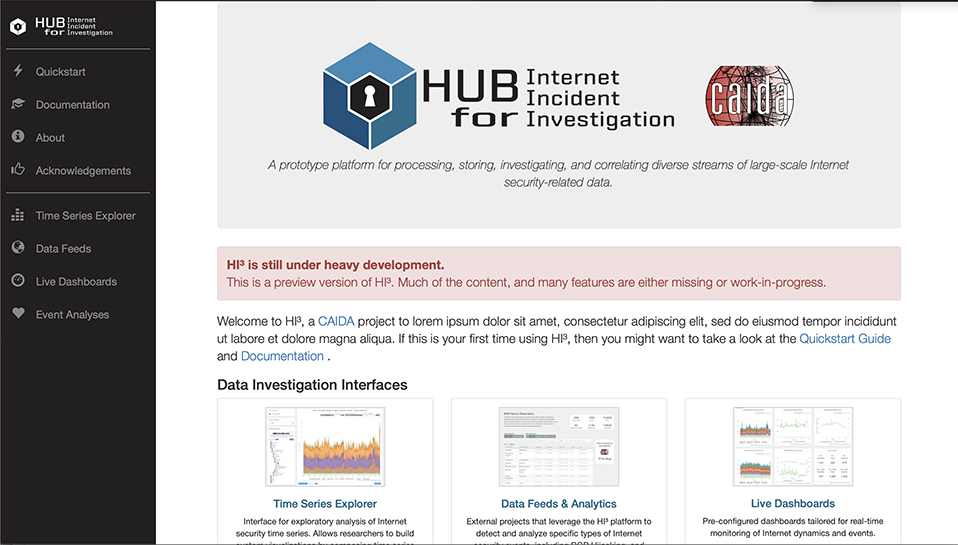
GRIP (preview): The Global Routing Intelligence Platform detects and visualizes attacks to the Internet global routing system in near-realtime through inference techniques that combine diverse datasets. |
STARDUST: making Network Telescope data streams and infrastructure easily accessible to students and researchers. |
Teaching
Spring 2026, Fall 2022, 2023, 2024: Computer Networks (CS 6250) / Computer Networking II (CS 4251)Spring 2026: Vertically Integrated Projects: IODA
Spring 2025: Computer Networking I - CS 3251
Spring 2024, 2023, 2022: Internet Data Science (CS 8803)
PhD Students and PostDocs
For a full list of students and alumni visit our lab's site at inetintel.orgCurrent:
Iliana Xygkou, GATech Ph.D. student
Olivier Bemba, GATech Ph.D. student
Weili Wu, GATech Ph.D. student
Zahra Yazdani, GATech Ph.D. student
Zhiyi Chen, GATech Ph.D. student
Former:
Ramakrishna Padmanabhan, UC San Diego PostDoc → Scientist at Amazon AWS Research
Alex Gamero-Garrido, UC San Diego Ph.D. student → PostDoc at Northeastern University → Asst. Prof. UC Davis
Shuai Hao, UC San Diego PostDoc → Asst. Prof. Old Dominion University
Jae Hyun Park, UC San Diego M.S. → Microsoft Azure Networking
Karyn Benson, UC San Diego Ph.D. → Akamai
Chiara Orsini, UC San Diego PostDoc → Amazon
Ojas Gupta, UC San Diego M.S. → VMware
Publications: in chronological order, by topic, by journal/conf/editorial
Other Professional Activities
- Editorial board member for: ACM SIGCOMM Computer Communication Review (2015-2018), IEEE/ACM Transactions on Networking (2017-2020)
- Steering Committee member for the TMA Conference 2018, 2017
- General chair for ACM CoNEXT 2018
-
TPC chair for: IMC 2025, PAM 2020, TMA 2014, Big-DAMA 2018, 2017
-
TPC member for: SIGCOMM 2024, ACM IMC 2025, 2024, 2023, 2022, 2020, 2019, 2013, PAM 2024, 2019 - 2014, ACSAC 2023, ACM CoNEXT 2017, IEEE ICC 2017 - 2014,
2007, TMA 2019 - 2012, IEEE ICNC 2013, IEEE Globecom 2012
- Other service in conference organizing committees: Ethics Committee and Travel Grant co-chair for IMC 2023; Poster Session co-chair for IMC 2022
-
Independent reviewer of projects and evaluator of project proposals for the European Commission
(Horizon 2020, FP7 ICT) and the US National Science Foundation
Funding
I gratefully acknowledge funding from the National Science Foundation, the US Department of Homeland Security, Cisco Systems, Comcast, ISOC, Google, the Open Technology Fund, and the US Department of State